
-
 Tourism plummets in US-blockaded Cuba
Tourism plummets in US-blockaded Cuba
-
Taylor Swift files to trademark her voice amid AI clone boom

-
 Trains collide outside Jakarta, killing four: officials
Trains collide outside Jakarta, killing four: officials
-
EU tells Google to open Android to AI rivals

-
 Italian Calzona quits as Slovakia coach
Italian Calzona quits as Slovakia coach
-
21 killed in deadliest Colombia bombing in decades

-
 Hazlewood, Kumar spark Delhi collapse as Bengaluru romp to victory
Hazlewood, Kumar spark Delhi collapse as Bengaluru romp to victory
-
UN maritime agency rejects Hormuz tolls

-
 Human Rights Watch warns of 'exclusion and fear' at World Cup
Human Rights Watch warns of 'exclusion and fear' at World Cup
-
Tuareg rebels in control of key Mali town after offensive

-
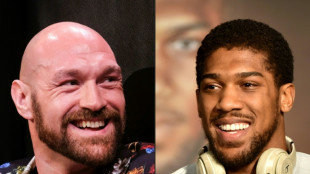 Joshua signs deal to face Fury in all-British grudge match
Joshua signs deal to face Fury in all-British grudge match
-
Melania Trump slams Kimmel joke likening her to an 'expectant widow'

-
 Carney launches $18 billion Canada sovereign wealth fund
Carney launches $18 billion Canada sovereign wealth fund
-
Modric suffers fractured cheekbone, will go under the knife: AC Milan

-
 'Looming' risk of nuclear arms race, UN proliferation meeting hears
'Looming' risk of nuclear arms race, UN proliferation meeting hears
-
Suspect due in court over shooting at Trump gala

-
 Sabalenka downs Osaka to reach Madrid Open quarter-finals
Sabalenka downs Osaka to reach Madrid Open quarter-finals
-
'Nobody is better than us' says Luis Enrique as PSG prepare for Bayern

-
 Hridoy, Shamim pull off record home chase for Bangladesh against NZ
Hridoy, Shamim pull off record home chase for Bangladesh against NZ
-
Thrilling Kvaratskhelia hoping to drive PSG to another Champions League final

-
 Swiss canton votes with centuries-old show of hands
Swiss canton votes with centuries-old show of hands
-
Mali attacks kill defence minister, deepening security crisis

-
 How remarkable Sawe made marathon history in London
How remarkable Sawe made marathon history in London
-
British Open to be staged at Royal Lytham and St Annes in 2028

-
 Mbappe doubt for Clasico after Real Madrid confirm thigh injury
Mbappe doubt for Clasico after Real Madrid confirm thigh injury
-
Salah will get fitting Liverpool farewell despite injury, says Van Dijk

-
 African players in Europe: Injury may end Salah's Liverpool reign
African players in Europe: Injury may end Salah's Liverpool reign
-
China blocks Meta's acquisition of AI firm Manus

-
 US woman speaks of ordeal in France Al-Fayed trafficking probe
US woman speaks of ordeal in France Al-Fayed trafficking probe
-
French teen faces jail in Singapore for licking vending machine straw

-
 Iran FM blames US for failure of talks after landing in Russia
Iran FM blames US for failure of talks after landing in Russia
-
Steep mountainside offers respite for daring Afghans

-
 Teenage wonder Sooryavanshi says criticism 'affects me a bit'
Teenage wonder Sooryavanshi says criticism 'affects me a bit'
-
Japan startup seeks approval of cat kidney disease treatment

-
 Technician dies installing stage for Shakira concert in Rio
Technician dies installing stage for Shakira concert in Rio
-
Cut off from the West, Muscovites rediscover Russian 'roots'

-
 'Joint venture in reverse': foreign carmakers seek edge with China partners
'Joint venture in reverse': foreign carmakers seek edge with China partners
-
Nations backing fossil fuel exit 'a new power': conference host Colombia

-
 Rockets thrash Lakers, Wembanyama triumphant on Spurs return
Rockets thrash Lakers, Wembanyama triumphant on Spurs return
-
ECB set to hold rates steady with eye on Iran crisis

-
 Team-first Kane propelling Bayern to glory as PSG showdown looms
Team-first Kane propelling Bayern to glory as PSG showdown looms
-
Pogacar vows to keep going until Seixas 'destroys' him

-
 From Adele to Raye, the UK school nurturing future stars
From Adele to Raye, the UK school nurturing future stars
-
Final talks begin on missing piece for pandemic treaty

-
 Oil rises, stocks swing as peace talk hopes wobble
Oil rises, stocks swing as peace talk hopes wobble
-
'Heartbroken' Xavi Simons out of World Cup and Spurs relegation fight

-
 North Korea's Kim reaffirms support for Russia's 'sacred' Ukraine war
North Korea's Kim reaffirms support for Russia's 'sacred' Ukraine war
-
Spurs win in Wembanyama return to take 3-1 lead over Trail Blazers

-
 As some hijabs come off in Iran, restrictions still in place
As some hijabs come off in Iran, restrictions still in place
-
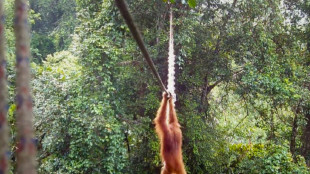
Orangutan uses Indonesia canopy bridge in 'world first': NGO

New Year’s Cybersecurity Resolution: 5 Questions to Identify and Mitigate Hidden Security Threats
PHILADELPHIA, PA / ACCESS Newswire / January 29, 2025 / While mass outages like 2024's CrowdStrike event can bring small businesses and major corporations alike to their knees, small technical issues or IT events are far more common and can shut down business functions with equally devastating effects. Cybersecurity threats raise the stakes even more, especially for small- and mid-sized businesses that rarely have strong protections in place to stave off potentially business-ending attacks.
"Surging security and cybersecurity threats don't discriminate by company size, industry, or geographic footprint. In today's high-risk security environment, an attack is all but inevitable," says Erik Eisen, CEO of CTI Technical Services, a leading provider of IT support and cybersecurity services. "Which is why every business today needs to make-and keep-a resolution to start the year with an evaluation of their network and security status to identify and address areas of weakness so they're around next year."
A Threatening Environment
According to a recent survey by New Relic, the median number of annual outages among respondents was 232, with more than half experiencing weekly low-impact disruptions. IT teams spend 30% of their time-the equivalent of 12 hours per 40-hour workweek-addressing interruptions ranging from network failures and third-party service issues to human error.
Cyberattacks are also surging, and small businesses are a favorite target. Attacks against small businesses increased by 150% over a two-year period at an average cost per incident ranging from more than $825 to nearly $654,000. More than 73% of US small business owners reported a cyberattack in 2023, most of which compromised user credentials. Further:
Financial motives are behind 98% of cyberattacks on small businesses.
System intrusion, social engineering, and basic web application attacks represent 92% of all small business breaches.
An average small business with less than 100 employees will receive 350% more social engineering attacks than larger enterprises.
"Despite the risk, the typical small business spends less than $500 a year on cybersecurity, and most don't have a dedicated cybersecurity budget," says Eisen. "It's an oversight that can have significant repercussions, as 60% of the small businesses that fall victim to cyberattacks close their doors within six months, unable to recover from the resulting downtime, reduced productivity, and remediation costs."
According to Nationwide claims data, it takes an average of 279 days for a small business to recover from a cyberattack, and the average associated costs are between $15,000 and $25,000. Further, 32% of small business owners who experienced an attack said it led to losing customer trust.
A Proactive Stance
When it comes to IT events and cybersecurity attacks, it is a matter of when, not if, for businesses of all sizes. However, there are several steps companies can take to mitigate their risk, starting with a self-assessment to determine areas of vulnerability. This doesn't require an IT expert; just answers to a handful of questions in the following five areas:
Staff training: is your team trained in cybersecurity best practices, including recognizing phishing attempts and the need for strong passwords, and is this training updated regularly?
Security safeguards: Are security measures in place that minimize human errors (e.g., email filters, browsing restrictions, multi-factor authentication, etc.), particularly around personally identifiable information (PII) access? Are they kept current?
Software patches and updates: Are procedures in place for installing the latest patches and updates to software and systems to protect against emerging threats and harden existing vulnerabilities? Are they followed?
Vendor security profiles: Do vendors, partners, and any other entity that may access the company's systems have proper cybersecurity and security protocols to prevent a breach on their end from impacting your operations?
Business continuity: Is a business recovery and continuity plan in place to get operations back up and running after a breach? Is it regularly reviewed and updated as needed? Are staff aware of the plan and trained in its deployment?
Responses will help determine if broader protections are required and if engaging with an IT service provider is warranted. If it is, look for a provider with cybersecurity experience that offers, at minimum, proactive monitoring, regular security assessments, and staff training. Prospective partners should also have a deep understanding of industry-specific compliance requirements.
Along with the above, CTI delivers:
Comprehensive services: CTI provides a wide range of technical services, including cybersecurity, data recovery, and workplace solutions.
Personalized customer support: CTI emphasizes building long-term relationships with clients by tailoring their services to specific needs, ensuring a personalized and customer-focused approach.
Advanced technological expertise: CTI strongly emphasizes staying ahead of technological trends, leveraging cutting-edge tools and processes that outperform older or less adaptive technology.
Transparent pricing and policies: CTI maintains a clear, upfront pricing structure and offers fair service terms with no hidden fees or complicated contracts.
Nationwide reach with localized support: CTI serves clients nationwide while maintaining a local, approachable touch that provides flexibility and scale.
Finally, during the evaluation process, be sure to ask prospects about their response times and disaster recovery capabilities and obtain-and check-references.
"Security and cybersecurity protocols don't have to break the bank, but they do need to be a budget priority," says Eisen. "Many policies can be implemented internally. For those that can't, the right IT partner will have the skills, experience, and flexibility to lower your risk profile in 2025 and beyond."
For more information on CTI's security and cybersecurity services, visit ctitechnicalservices.com.
About CTI Technical Services
CTI Technical Services is a trusted IT service provider specializing in network design, information architecture, and comprehensive IT support for clients nationwide. With expertise in serving dental and health practices, hospitality, small businesses, and golf courses, Philadelphia-based CTI offers a full suite of services, including managed IT services, cybersecurity, cloud solutions, telecommunications, and network infrastructure design and implementation. Committed to security, efficiency, and reliability, CTI ensures that every client's technology is optimized to protect their business and support seamless operations. For more information, visit ctitechnicalservices.com.
Media Contact:
Liz Goar
NPC Creative Services
[email protected]
SOURCE: CTI Technical Services
View the original press release on ACCESS Newswire
T.Ward--AMWN

