
-
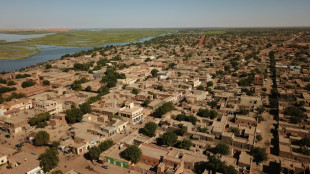 Gunfire in Mali as army battles 'terrorist groups'
Gunfire in Mali as army battles 'terrorist groups'
-
Gunfire rocks Mali districts, including junta stronghold: witnesses
-
 Welsh football icon Ramsey takes on marathon challenge for charity
Welsh football icon Ramsey takes on marathon challenge for charity
-
Aussie Rules fires appeals chair over ruling on anti-gay slur

-
 Lakers' OT win puts Rockets on brink of NBA playoff elimination
Lakers' OT win puts Rockets on brink of NBA playoff elimination
-
From radiation to invasion: a Chernobyl worker's two wars

-
 AI firms flex lobbying muscle on both side of Atlantic
AI firms flex lobbying muscle on both side of Atlantic
-
First female Archbishop of Canterbury to meet Pope Leo

-
 Hundreds of firefighters battle Japan forest blazes
Hundreds of firefighters battle Japan forest blazes
-
Lakers down Rockets in overtime for 3-0 series lead, Celtics hold off Sixers

-
 US envoys heading to Pakistan for uncertain Iran talks
US envoys heading to Pakistan for uncertain Iran talks
-
'Hockey is religion': Montreal fans pack church for playoff push

-
 Billionaire Elon Musk enters courtroom showdown with OpenAI
Billionaire Elon Musk enters courtroom showdown with OpenAI
-
Crunch nuclear proliferation meeting at UN amid raging global wars

-
 Awkward debut for Trump at correspondents' dinner
Awkward debut for Trump at correspondents' dinner
-
Under blackout threat, Wikimedia reaches compromise with Indonesia

-
 'Going to the moon': Irish footballers return to China 50 years after historic tour
'Going to the moon': Irish footballers return to China 50 years after historic tour
-
Spurs' Wembanyama ruled out of game 3 after concussion

-
 Palestinians to vote in first elections since Gaza war
Palestinians to vote in first elections since Gaza war
-
Pragmatism, not patriotism, pushes young Lithuanians to military service

-
 Group Seeking Court Order to Halt CMS Medicare THC Hemp Marijuana Program
Group Seeking Court Order to Halt CMS Medicare THC Hemp Marijuana Program
-
Peru confirms election runoff date, court says no to Lima re-vote

-
 Venezuela, Colombia pledge military cooperation on first post-Maduro visit
Venezuela, Colombia pledge military cooperation on first post-Maduro visit
-
US hopes for progress, but Iran says not direct talks

-
 Maine governor nixes data center moratorium in state
Maine governor nixes data center moratorium in state
-
Betis's Bellerin further dents Real Madrid title hopes

-
 Lens rally but title bid fades after draw at Brest
Lens rally but title bid fades after draw at Brest
-
OpenAI CEO apologizes to Canada town for not reporting mass shooter

-
 UK PM vows legislation to ban Iran Guards: report
UK PM vows legislation to ban Iran Guards: report
-
Leipzig tighten top-four grip as Union's Eta suffers second loss

-
 Furyk named USA captain for 2027 Ryder Cup
Furyk named USA captain for 2027 Ryder Cup
-
EU, US sign critical minerals plan to counter China reliance

-
 The 'housewives' did well -- Ukraine takes drone know-how abroad
The 'housewives' did well -- Ukraine takes drone know-how abroad
-
Court removes US businessman from managing his Brazilian football team

-
 'Natural' birth control risks unwanted pregnancy, experts warn
'Natural' birth control risks unwanted pregnancy, experts warn
-
No.2 Korda boosts LPGA Chevron lead to seven

-
 EU trade chief seeks 'positive traction' on US steel tariffs
EU trade chief seeks 'positive traction' on US steel tariffs
-
Anthropic says Google to pump $40 bn into AI startup

-
 Kohli makes Gujarat pay as Bengaluru cruise to IPL win
Kohli makes Gujarat pay as Bengaluru cruise to IPL win
-
One injured in bomb attack on Colombia military base

-
 Envoys from Iran, US expected in Pakistan for new talks
Envoys from Iran, US expected in Pakistan for new talks
-
ILO names US official as number two amid grumbling over unpaid dues

-
 Son of director Rob Reiner pays tribute to slain parents
Son of director Rob Reiner pays tribute to slain parents
-
AI united Altman and Musk, then drove them apart

-
 Sinner overcomes Bonzi in record hunt at Madrid Open
Sinner overcomes Bonzi in record hunt at Madrid Open
-
Havana property market stirs as investors bet on political change

-
 Children's lives at risk from US funding cuts to vaccine alliance: CEO
Children's lives at risk from US funding cuts to vaccine alliance: CEO
-
Brazil's Lula has surgery to remove skin lesion from scalp

-
 Defending champion Alcaraz to miss French Open with wrist injury
Defending champion Alcaraz to miss French Open with wrist injury
-
Battle lines drawn over EU's next big budget


The New Age of Infiltration and the Collapse of Firewall-Based Security
NEW YORK, NY / ACCESS Newswire / November 21, 2025 / Around the world, nations are discovering that security now has two fronts. The physical front that protects borders, and the institutional front that protects trust. Governments poured resources into the first. The second has been left exposed. Institutions built on access and openness are now confronting threats that move quietly, slowly, and deliberately. They don't break rules. They use them. And that shift has created a global demand for a new kind of defense.
The exact type that SMX (NASDAQ:SMX) provides. Its technology closes the blind spots adversarial actors have exploited for years. The company has long warned that the next wave of security breaches would merge physical infiltration with digital manipulation, and today's patterns confirm that warning with precision.
Notably, these vulnerabilities aren't tied to any one country or ideology. They come from structural weaknesses in open systems built on participation and trust. That trust worked when threats were external, obvious, and easy to isolate. It doesn't hold when influence can hide inside the routines of institutional life. The infiltration of today is about access, not intrusion.
In other words, the compromise can be subtle. It doesn't trigger alarms or violate protocols. It enters through the everyday materials that move through supply chains, slipping in through components, parts, and products that appear routine. Once inside, it blends into operations until familiarity becomes its camouflage. That's the problem.
Most institutions lack the tools to verify where those materials truly originate, how they were handled, or whether they carry hidden vulnerabilities. SMX, now gaining deal traction across continents, is helping companies, institutions, and governments ensure those vulnerabilities never reach the point of catastrophe.
Where Physical Inputs and Digital Systems Converge
That protection starts with the obvious. Every modern threat begins with the physical. Bad actors understand that the easiest path into an institution is not through code or policy, but through the materials used. A single compromised component can enter a factory, a data center, a government lab, or a defense contractor long before cybersecurity systems ever activate. Once inside, that material becomes a trusted object, and trust becomes the attack surface.
From there, infiltration evolves. A corrupted chip can alter data. A counterfeit sensor can distort measurements. A compromised module can open digital pathways that no firewall was built to monitor. Physical infiltration becomes digital influence, and digital influence becomes institutional vulnerability. The chain starts with materials and ends with systems that no longer know what to trust.
This merger of physical access and digital impact is the defining threat of the modern era. It's not dramatic. It's procedural. It uses supply-chain familiarity to validate inputs, and those inputs to manipulate downstream information and operations. To truly be secured, that chain must be fortified at every link. SMX provides the technology to do that.
The SMX System is Built for Both Dimensions of Modern Security
SMX secures the physical world by giving materials, documents, and products a molecular identity. It embeds memory and provenance into the item itself. It can be gold, rubber, liquids, or textiles. Virtually any material can benefit. Once embedded, tampering becomes impossible to hide. Counterfeits become easy to expose. Origins remain inseparable from the objects they belong to.
This has always been SMX's foundation, and as new threats emerge, its technology is showing it can be an essential part of global stability protocols. No, SMX cannot control what people think. But it can eliminate the deception that enables influence. It verifies the provenance of the materials, credentials, and hardware entering a system, making manipulation transparent and infiltration visible. That is how it defends. And by securing every link in the chain, that capability becomes the impenetrable piece of the arsenal that protects both critical assets and the people who depend on them.
About SMX
As global businesses face new and complex challenges related to carbon neutrality and meeting governmental and regional regulations and standards, SMX can offer players along the value chain access to its marking, tracking, measurement, and digital platform technology to transition more successfully to a low-carbon economy.
Forward-Looking Statements
This editorial contains forward-looking statements that involve significant risks and uncertainties. These statements reflect current views regarding the potential use of SMX technology to enhance institutional integrity, strengthen verification systems, and reduce the risk of infiltration by bad actors or nefarious networks. Forward-looking statements include, but are not limited to, statements regarding anticipated improvements in institutional security, the possible adoption of molecular-level verification, the ability of SMX systems to protect credentials, documents, or access pathways, and the broader market or regulatory conditions that may influence demand for such solutions. These statements are based on assumptions that may prove inaccurate and are subject to factors that are difficult to predict. Actual results may differ materially from those expressed or implied due to a range of uncertainties, including changes in government policy, evolving threat landscapes, institutional readiness, regulatory considerations, funding cycles, technological constraints, and other risks detailed in SMX's filings with the Securities and Exchange Commission.
Forward-looking statements speak only as of the date of this editorial. Readers should not place undue reliance on them. SMX undertakes no obligation to update or revise any forward-looking statements to reflect new information, future events, or changes in circumstances except as required by law. The purpose of this content is to explore potential applications of verification technologies within institutional environments. Nothing in this editorial should be interpreted as a guarantee of future performance or a prediction of specific security outcomes.
EMAIL: [email protected]
SOURCE: SMX (Security Matters) Public Limited
View the original press release on ACCESS Newswire
Th.Berger--AMWN